Return-To Email Scam
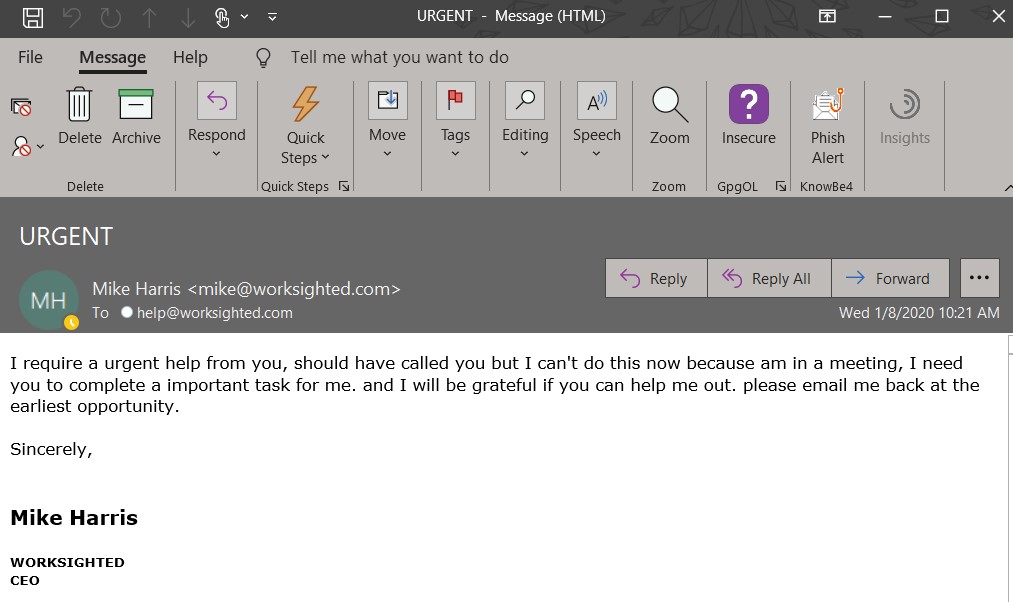
What exactly does an e-mail scam look like? While they can vary in how they appear, the most common scams have become easy to detect. Here at Worksighted, we have seen a number of scams recently that take advantage of a function of email. We are calling these “return-to” scams. How this appears to the user is in an email that looks like it is from an internal email address. The sender is usually asking for an urgent favor or task.
The email will look like this:
When you hit reply, see what happens:
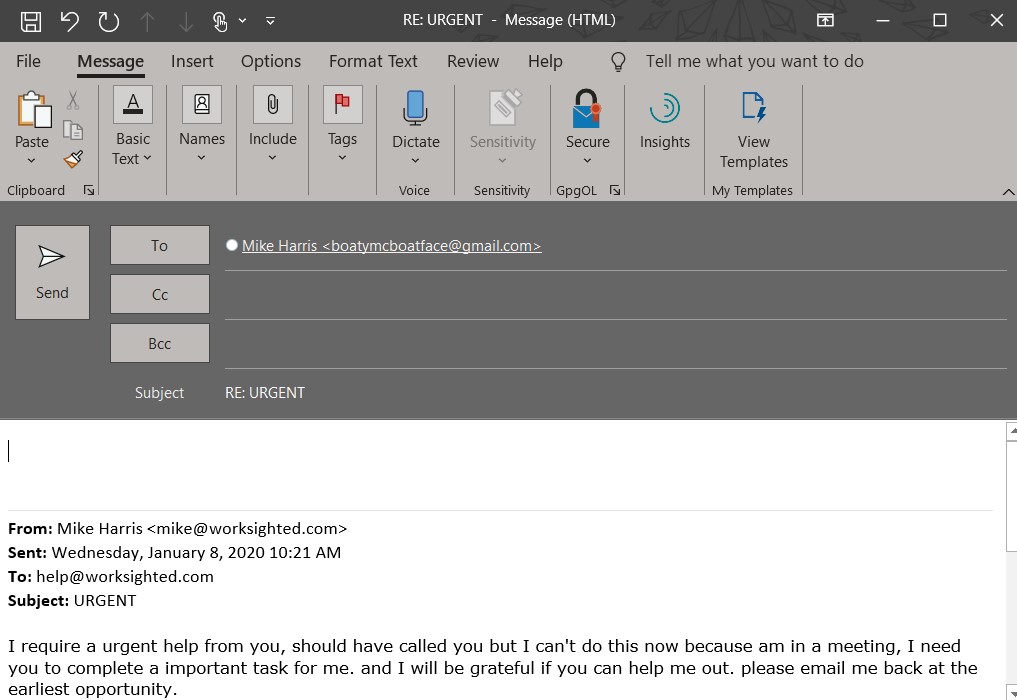
Notice that the “To” box changed to a Gmail account.
This is because of a feature of email that allows someone to send from one address, and receive replies at another address and is a sure tell sign that it is a scam. These emails can alarm many users because if the user detects that the context of the email is a scam, they may believe that the sender’s email account has been compromised. However, in the case of these types of emails, the internal sender’s account is safe.
Worksighted is always happy to review emails like these. We can easily purge an email like this from all internal mailboxes, to prevent anyone from replying and getting pulled into a scam.
Note that these scams always end up asking for gift cards. Please never respond to any e-mailed requests for gift cards. You should never buy gift cards based on an emailed request, and your employer should ensure that they never make valid requests for gift card purchases without in-person confirmation.
So, whether you are a pro at spotting suspicious red flags in your email, or you are just starting to get curious about how to protect your accounts, it’s important to stay updated on the most recent scams. If you want to dig a little deeper into boosting your security, check out this article on other email-based security threats. As always, if you run into something that you presume is above your head or a severe security risk, reach out to Worksighted and our awesome team members will be happy to assist your company in navigating potential cyber threats.