The 3 Steps to Overcome Remote Working Security Issues
In a post-COVID world of remote and hybrid working, your security will have to work harder to keep your organization protected, as a dispersed workforce poses new security challenges. And what’s more, the cybersecurity threat is ever-evolving, so the only way to overcome remote working security issues is to cover all bases.
Many organizations will find that hybrid working, where employees alternate between days at home and days at the office, will soon become the norm. The same remote working security challenges apply for hybrid working too. So, with no time to lose, let’s get started and make sure you are putting in place the correct measures to keep your corporate data safe.

The Main Remote Working Security Issues Today
For many organizations, the COVID-19 pandemic has led to a sudden roll out of devices and collaboration apps to facilitate remote working. With business continuity the priority, keeping teams productive and in contact with each other has been the main concern. Yet, unleashing productivity for remote workers must always be balanced with robust security.
Cybersecurity risks grow in a remote working setting. Cybercriminals are looking to exploit any vulnerabilities that arise when technology is taken outside the safeguard of the organization’s firewall. For instance, Deloitte reported that there were 500,000 instances of attacks targeting video conferencing tools between February and May 2020.
But the increased threat from home working takes many forms. It may come from surprising sources – for instance, disgruntled or opportunistic employees who feel emboldened by the lack of supervision to attack their own organizations. It could arise because of Bring Your Own Device (BYOD) policies, where more employees are accessing the network on devices which may lack sophisticated security software. Cybercriminals know this and are out to exploit these circumstances.
How to Overcome Remote Working Security Challenges
Employee Training
Phishing is still the most common cybersecurity threat – where cybercriminals attempt to trick users into clicking on malicious links and files or into providing personal information. This is usually carried out by sending sophisticated emails direct to inboxes.
Training remains the best way to counteract these attacks. Simulations can be created to test users’ abilities to spot phishing attacks. Going over the basics, such as password strength, is still as important as ever. The best security requires covering all the bases.
The “Zero Trust” Security Model
Remote working requires a new approach to security, and a move away from what was often called a “castle and moat” approach. The idea being that the castle’s defences are strong and impenetrable from the outside. But if you’re inside you can be trusted with the keys to the castle. Likewise, once safely within the physical walls of the office, with the protection of firewalls and security systems, you can be given access to the network.
With employees working from dispersed locations, this approach falls apart. The Zero Trust approach is centered on trusting no one, whether you are in the castle or not. At the core of Zero Trust security is multifactor authentication (MFA). Regardless of physical or network location, users will have to type in a passcode sent to their phone, for example. From a user-perspective, this has become an accepted experience as they are used to it in other contexts, for example, confirming their identity when making a banking transaction.
Get Help From the Experts
The best response to any remote working security issues is a holistic one. With many different ways for cybercriminals to attack, it will always make sense to take an approach that covers as many bases as robustly as possible. Yet, this will be different for every organization.
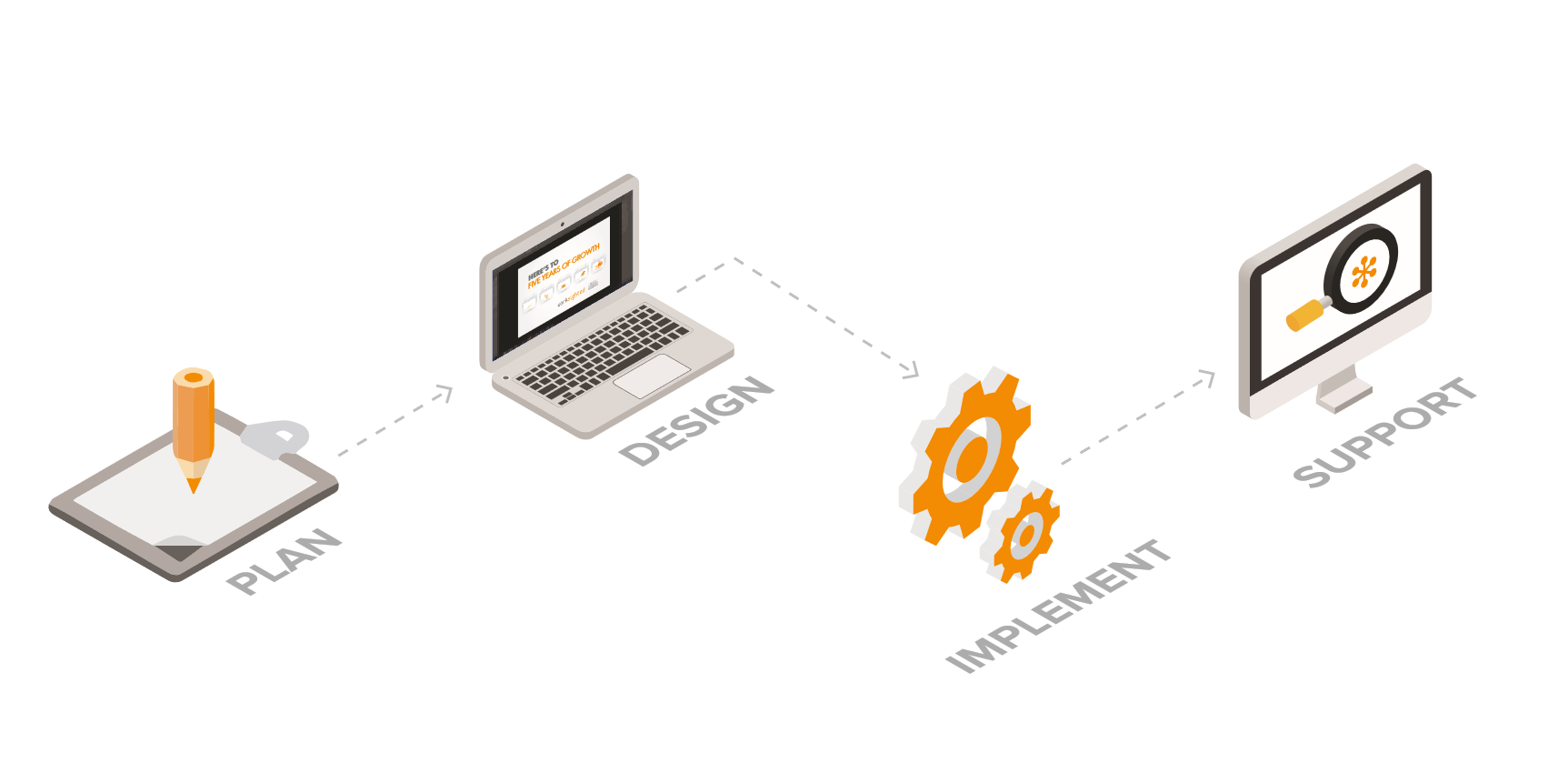
The expertise and experience needed to make the right kinds of decisions – and then to apply them to your IT environment – for your unique requirements is perhaps best served by a third party. Managed security services can provide dedicated support for remote working, often more efficiently and cheaper than achieving the same level of security with internal teams.
Robust Security for Remote Working
Worksighted has an expert cybersecurity team that can work closely with you to deliver a secure remote or hybrid IT environment tailored for your specific business needs. The Worksighted Security Essentials service offers the complete cybersecurity package including: Identify, Protect, Detect, Respond, and Recover. With remote working security challenges it is important to be proactive, and our approach ensures that you stay one step ahead of the latest threats.
The best place to start is with a free 60-min exploratory consulting engagement with a member of the Worksighted team. We’ll provide a professional review of your remote working security challenges, IT roadblocks, and opportunities to help improve your cybersecurity set up. This way we can begin to outline a strategy to ensure that any remote working security issues are taken care of.
To learn more about remote working security issues, get in contact with the Worksighted team today.